AGENDA
This year’s CIO Summit program has been designed as a coherent, strategic narrative reflecting the realities of an IT leader’s role in 2026. We have focused on debates, contrasting perspectives, and practitioner-led discussions. As a result, we go beyond traditional presentations to provide a comprehensive view of the challenges, decisions, and responsibilities today’s CIOs face.
April 22, 2026
CIO Summit
One Day Event
Registration & Welcome Coffee
Welcome & Opening
The official opening of CIO Summit Poland 2026, introducing the key themes of this year’s edition. The session will outline the strategic context of the event, highlight the most pressing challenges facing IT leaders in 2026, and present the main topics that will be explored in the subsequent agenda blocks.

Radek Brzózka
Science journalist, technology enthusiast, and television presenter, Telewizja Polska
CIOs Leading the AI Supercycle – Life Beyond Efficiency
As organizations accelerate digital investment, CIOs face a complex set of challenges: modernizing legacy systems, addressing rising technical debt, embedding cybersecurity, ensuring regulatory compliance, and preparing their workforce for technology-driven change. IDC research shows that nearly 40% of CIOs expect to overspend on digital infrastructure within the next 18 months, with technical debt cited as a primary driver, while only a fraction of digital initiatives deliver measurable business impact. At the same time, global digital transformation spend is set to surpass $4 trillion by 2027, underscoring the urgency for CIOs to deliver value, not just investment.
Lapo Fioretti | IDC
Senior Research Analyst, EMEA AI-Fueled Business Strategies


Lapo Fioretti
Senior market intelligence analyst with 6+ years of experience specializing in emerging technologies, digital economy, and regulatory impacts. Proven expertise advising C-suite executives and technology vendors on strategic market entry, investment, and digital transformation. Skilled in delivering actionable insights, driving go-to-market strategies, and leading client engagements that support business growth and innovation.
Event Sessions
One Day Event 9:10 am
CIOs Leading the AI Supercycle – Life Beyond Efficiency
As organizations accelerate digital investment, CIOs face a complex set of challenges: modernizing legacy systems, addressing rising technical debt, embedding cybersecurity, ensuring regulatory compliance, and preparing their workforce for technology-driven change. IDC research shows that nearly 40% of CIOs expect to overspend on digital infrastructure within the next 18 months, with technical debt cited as a primary driver, while only a fraction of digital initiatives deliver measurable business impact. At the same time, global digital transformation spend is set to surpass $4 trillion by 2027, underscoring the urgency for CIOs to deliver value, not just investment.
Architecture of Freedom – How Technological Sovereignty Becomes the Foundation of Strategy
In a world of escalating hybrid conflicts, technological sovereignty is becoming the foundation for the survival of every organization’s digital fortress. The Sovereignty by Design approach enables organizations to regain real control over their data and infrastructure, eliminating risks associated with unpredictable jurisdictions and global dependencies.
In this session, we will explore how to turn digital autonomy into a strategy that ensures long-term business continuity in the face of geopolitical disruption. This is not just about security — it is a critical insurance policy, ensuring that when it matters most, you retain the keys to your own kingdom.
This is not a choice between innovation and isolation, but a deliberate approach to designing security that guarantees resilience in an unpredictable world.

Jakub Łukasiewicz
Regional Sales Director, HCL Software | CEE
Board Perspective: What Does the Business Expect from CIOs This Year? + Q&A
This time, the CIO does not take the floor — the CIO becomes the subject of the discussion.
On stage, CFOs, COOs, CROs and CEOs will share their perspectives. They work with technology leaders every day and have well-formed and not always comfortable opinions. What does the board really expect from the CIO in the era of AI? How do they assess the CIO’s role in shaping key business decisions? When does a CIO become a true strategic partner, and when do they remain a highly capable executor of others’ plans?
This panel offers a rare opportunity to hear a perspective that usually remains behind closed boardroom doors – candid, thought-provoking, and relevant for both technology and business leaders.

Jacek Nawrot
Senior ICT Executive, IDC

Robert Cegliński
Vice President of the Management Board, Chief Risk Officer, PayPo

Aneta Gawrońska
Chief Financial Director, Medicover Sport

Monika Kozakiewicz
CEO, NAUTA Shiprepair Yard

Diana Skotnicka
CFO, Respect Energy Holding
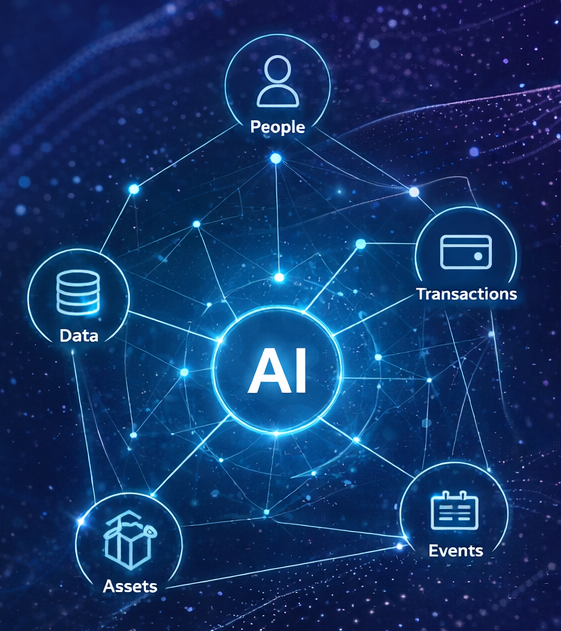
Stopping Fraud Before It Starts: Identity Intelligence Meets Agentic AI
Professionals across industries are in search for solutions to effectively prevent fraud while ensuring legitimate customers never feel the friction of fraud prevention. This requires combatting account takeover, unauthorized access, and new account fraud by integrating fraud prevention directly into the user journey. Many times, this involves incorporating friction when and where it is needed by building adaptive user journeys that evaluate and act on risk signals at key points such as registration, login, profile management, and transaction (either payment, check-out or subscription activation).

Marcin Zimny
Principal Solutions Architect, Ping Identity

Andrei Dumitru
Executive Partner, IT Smart Systems
CIO’s Challenges in 2026 + Q&A
The role of the CIO has never been more strategic and never more demanding.
Transforming IT into a true business partner, leveraging AI as a source of real competitive advantage, building cyber-resilience as an operational foundation, and scaling innovation securely across complex organizations, these are the challenges technology leaders face every day.
CIOs from different industries come together for an honest conversation about what truly defines effective technology leadership in 2026.
Moderator

Lucyna Michniewicz-Ślaska
CIO, VOX Group

Rafał Zbiróg
Group CIO, Inter Cars

Tomasz Bednarczuk
CIO, Kaczmarski Group

Robert Tomaka
CIO, Diagnostyka

Alicja Rybczyńska
Chief Information Officer, Veolia Poland
Turning CIO Challenges into Measurable Outcomes with Oobeya
CIOs can transform today’s most pressing challenges, ranging from AI adoption and fragmented data to lack of execution visibility into measurable business outcomes. By leveraging engineering intelligence, Oobeya connects data across the software development lifecycle, turning insights into actionable decisions. Attendees will discover how to identify bottlenecks, align technology with business goals, and drive continuous improvement without manual reporting. The talk highlights a practical approach to moving from insight to execution, enabling CIOs and CTOs to deliver real, scalable impact in the age of AI.

Şükrü Çakmak
CTO & Co-Founder, Oobeya
Coffee Break & networking
The Private AI Paradigm
This session unveils Cloudera’s Private AI Anywhere, a sophisticated framework designed to bring high-performance intelligence directly to your data, regardless of whether it resides in the cloud, the data center, or at the edge.
We will explore a comprehensive architecture that empowers organizations to build and scale AI applications with absolute, end-to-end governance over every model, agent, and inference point.
Key Takeaways
Sovereignty & Compliance → Secure data and model integrity within the most rigorous regulatory environments.
Operational Excellence → Eliminate “cloud tax” and accelerate ROI by deploying enterprise AI at scale.
Unrivaled Portability → Experience the true flexibility of an “Anywhere Cloud” infrastructure.

Peter Rizvi
Territory Account Executive, Cloudera
Stochastic Mind: Evaluating Response Stability in Large Language Models
As organizations deploy language models in production environments, accuracy metrics alone are no longer sufficient. Equally important is the consistency of model behavior across different tasks. During this session, I will present the first results of a large-scale study on the consistency of language models, offering new insights into their application in agent-based systems. Conducted repeatedly under varying configurations, the study reveals not only what models get right, but also how reliable they are in practice—and where their consistency breaks down under real-world conditions. Attendees will gain a new perspective on selecting and evaluating language models, as well as a shared framework for discussing consistency as a key quality criterion in agent-based systems.

Dariusz Korzun
Director, Applied AI, Global Cloud Solution Architecture, PepsiCo
AI in Żabka’s communication – case study

Paweł Grabowski
Head of Digital B2B, Żabka Group
How does spatial AI open up a new dimension of business opportunities?
The development of AI, especially generative 2D models, is transforming the way marketing content is created. However, current tools do not address the challenges of scale and interactivity – two key issues for the fashion industry. During the session, we will discuss how leveraging 3D models can significantly reduce the cost of producing marketing materials and what new digital experiences we can expect in the near future.
Moderator

Radek Brzózka
Science journalist, technology enthusiast, and television presenter, Telewizja Polska

Maciej Borowski
Co-founder & COO, Pirxe

Przemysław Kadula
Co-founder & CBO, Pirxe
Leading Change for AI Adoption: Aligning Technology, Skills and Organization

Evghenia Iarina
Strategic Partnerships Director, Coursera
The CIO Mandate: Scaling Enterprise Intelligence and Business Value
In the Future of Work defined by Human & Machine Collaboration, IT Executives are the lead architects. They need to scale not only AI adoption, but more than ever also assure Business Outcomes, Security & Governance. Learn how Workday can accelerate this Transformation, act as an operational multiplier while seemlessly intetrating in your Business Platform Stack.

Jens Löhmar
CTO Continental Europe & DACH, Workday
AI Reality Check + Q&A
Every company is “doing something with AI” but what has it actually delivered?
Practitioners from retail, fintech, media, and industry take stock of three years of experimentation: what has proven to be a central element of the CIO’s strategy, what real AI management looks like – from governance and risk assessment to measuring ROI, and why moving from pilot projects to full-scale deployment has turned out to be more difficult than anyone expected.
A conversation about what has actually been done, not what should have been done.
Moderator

Ewa Zborowska
Research Director, IDC

Dariusz Korzun
Director, Applied AI, Global Cloud Solution Architecture, PepsiCo

Paweł Grabowski
Head of Digital B2B, Żabka Group

Małgorzata McCarthy
Technology Product Leader – Analytics, AI & Data, ManpowerGroup

Paweł Majek
Product Director, Poland Go To Market, Visa
Networking Lunch
Digital Transformation Exposes the True Capabilities of CxOs
Let’s be honest: most “digital transformations” are just cloud migrations, a new CRM, and a polished dashboard for the board.
The P&L doesn’t move. Customers don’t feel a difference. And 18 months later, someone asks: “So what did we actually gain?”
Meanwhile, the world has changed.
AI is making decisions – where does the human leader fit in?
Edge computing is pushing intelligence to the edge of the network.
Data flows in real time from factories, warehouses, and hospitals.
In this new reality, a CxO who is still “the head of IT” is like a sailboat captain on a highway – moving, but not in the right direction.
So let’s talk about it without the buzzwords:
→ Why “digital strategy” is an oxymoron (there is only one strategy: business strategy)
→ How AI and edge computing are reshaping the value chain
→ The new CxO capability: not managing IT, but orchestrating value

Robert Pławiak
CDIO/CTO, Polpharma

Agnieszka Bochacka
Global Digital Transformation Director, GE Healthcare
Technology Knockout: Finding Strategy in the Chaos
Digital arena, real challenges, and one key principle: the winner is the one who understands strategy best.
This presentation offers a perspective on the evolving world of technology and addresses the question of how to regain control amid chaos, AI pressure, and increasing complexity.
It is not a story about tools, but about mindset: how to stop “taking punches” and start building an advantage through a conscious, well-defined strategy.

Edyta Zborowska
Business Development Manager, vSoft
Technological sovereignty – strategy or necessity? + Q&A
Dependence on foreign technology providers is no longer solely an economic issue. In the face of rising geopolitical tensions and cyber threats, it has become a matter of national security. Poland and Europe now face a fundamental question: is building their own technological capabilities, sovereign computing infrastructure, and independent AI models a realistic strategy, or merely a political declaration?
Moderator

Jarosław Smulski
Senior Program Manager, Systems & Infrastructure Solutions, IDC

Radosław Maćkiewicz
Director Centre for Information Technology, Centralny Ośrodek Informatyki

Grzegorz Zalewski
CEO, Aplikacje Krytyczne

Wiesław Wilk
CEO, Polska Chmura

Wojciech Wilk
Regional Director, CEE, HCLSoftware

Artur Kurcweil
CISO / CSO, Bank Millennium
The Missing Layer Between AI Agents and Your Enterprise – Governance, Security & Operational Control in the Age of AI
Employees and AI agents are connecting to enterprise systems faster than security and governance teams can keep up. This session explores the emerging control gap, where agents access sensitive data, trigger actions, and consume resources without centralized oversight. Drawing from real enterprise experiences, we’ll walk through a practical architecture for a secure gateway layer that gives CIOs visibility, policy enforcement, and cost control across all AI tool usage – without slowing down innovation.

Marcin Mazurek
Co-Founder, Bitropy
Technology, Business, and People — How a Great CTO Brings Together Worlds That Can’t Be Separated

Ewa Zborowska
Research Director, IDC

Norbert Franke
CTO, Publicis Groupe Poland
Secure by Design – when security, infrastructure, and business speak with one voice + Q&A
Cybersecurity is no longer the sole domain of the IT department. Today it is a strategic foundation of the entire business, challenged by AI, regulation, and the growing complexity of hybrid environments. Panel participants will address key questions around resilience architecture, risk management, and building a culture of security in organizations that aim to treat cybersecurity not as a cost, but as a real competitive advantage.
Moderator

Marek Laskowski
CIO, Kancelaria Prawna Domański Zakrzewski Palinka

Marek Ługowski
Head of Infrastructure, Swiss Krono Group

Tomasz Kędziora
Dyrektor Departamentu Cyberbezpieczeństwa, CISO, P4

Przemysław Szulecki
Cyber Risk Senior Manager, HSBC
Simulation of Emotions by Artificial Intelligence: Care Algorithms in the Attachment Economy
Algorithms are, above all, a powerful social force. As technologies capable of simulating empathic responsiveness evolve, relationships with AI are becoming deeply engaging—especially for the youngest generations (AI Natives). AI companions encourage the exploration of new forms of intimacy and act as mechanisms reshaping existing structures of emotional relationships.
I will focus on the growing phenomenon of artificial companions and computer-generated influencers – anthropomorphic, hyper-realistic figures that simulate human experiences and emotions. The universe of virtual influencers and lovebots is shaping the worldview of the youngest generation growing up in an environment of synthetic media. Digitally embodied and socially interactive agents are taking on opinion-forming roles, while their operators deploy a wide range of influence techniques.
Empathy-simulating AI learns human responses, anticipates needs, and communicates in ways that, for younger users, can feel safer, more intuitive, and more desirable than interaction with other people. According to affective bonding theory, humans are predisposed to form emotional relationships not only with other humans but also with artificial entities-provided these fulfill social and communicative functions.
In this way, power in capitalism increasingly operates through emotional attachment.

dr Ada Florentyna Pawlak
Technology Anthropoligist,